The Best Fluffy Pancakes recipe you will fall in love with. Full of tips and tricks to help you make the best pancakes.
If you want to learn about 888 RAT then you are at the right place in this article you will learn about 888 rat and their use. In this article, you get a demo practical in LAN to make you understand it well.
What is a RAT?
Basically, a RAT stands for Remote Access Trojan is a malware or payload used to gain access to someone’s infected system. Once these rats are installed in someone’s system the attacker can get remote access after which he sends commands and receives the desired data as a response.
What is 888 RAT?
RATS are also known as trojans or payloads can be created using tools. Generally, payloads are created using Metasploit, Ngrok, etc. but 888 Rats is also a user-friendly tool used to create payloads with ease. It also has the feature to link Ngrok and Metasploit and use that to create rats.
How does this Rat campaign reach victims?
This particular campaign has been using fake Facebook profiles and other social media platforms to propagate the malicious app. The 888 RAT is usually masked as a legitimate piece of Android software, which the target downloads from a 3rd-party app-hosting site. The criminals use several profiles for the spam campaign. Some of these profiles pose as members of the tech community, while others act as Kurd supporters. Apart from promoting bogus apps delivering the 888 RAT, the same profiles were also used to spread phishing links for various social media apps and sites – such as Snapchat.
The 888 RAT is not a custom-built piece of malware. In fact, it was initially sold on a public website by its creators. It has been receiving regular updates, including An Android version that came out in 2019. It is not clear whether the Blade Hawk hackers are using a purchased copy or a cracked one. Regardless, the features of the malware remain the same.
How to Create a Rat?
To create a Rat we have to use tools and as our article is about 888 RAT so we will more focus on making payloads using this tool. So let’s start with the practical to use 888 RAT follow each step without skipping any step if you are a beginner.
I am doing this demo practical in my virtual system by disabling windows defender.
Step-1 (Downloading the Tool)
RAT is a paid tool but if you want to download a cracked tool then we can provide you with a link to download the cracked file.
To download cracked 888 RAT click here. It is a drive link and you can download it easily but remember to download this file by disabling the antivirus as the antivirus will detect it as a trojan and delete it.
Step-2 (Extracting)
Extract the file using any extracting tool like WinRAR and others. I have done it with 7zip. During the extraction, it will ask for a password to unlock the file. Fill the box with “www.masterscyber.com” as the password. It will automatically extract the file and will show the folder in the desired location which you have selected.
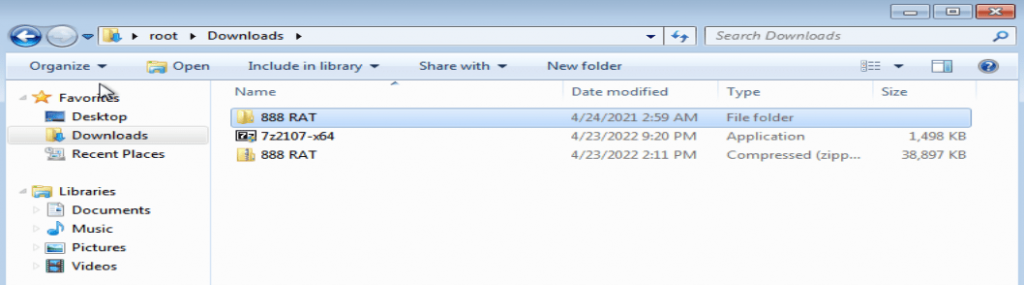
Step-3 (Opening)
Open the extracted file you will find the 888 RAT file open it. After that, you will have to do the installation. It will open its windows simply copy the code and save the code in a notepad and click ok.
The next window will open asking you to agree to the term and conditions. Click on agree and now the installation has been completed now it will open the tool within some minutes of time.

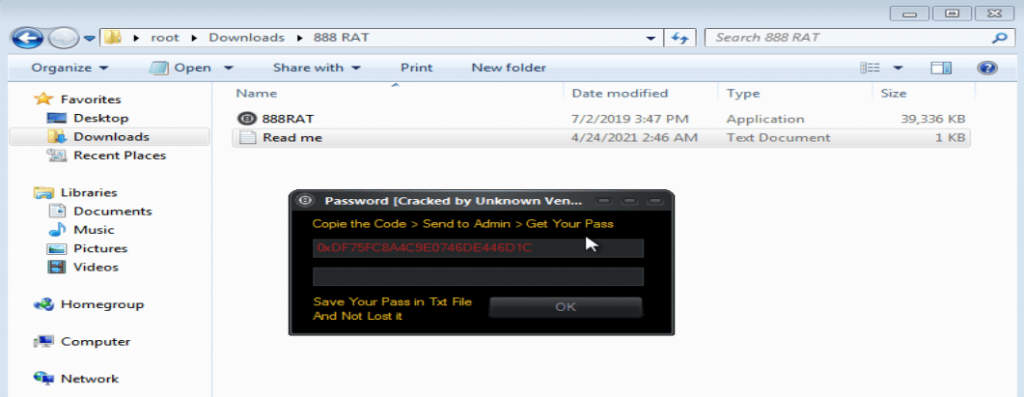
Step-4 (Overview)
Here you get the option to choose the OS for the payload.
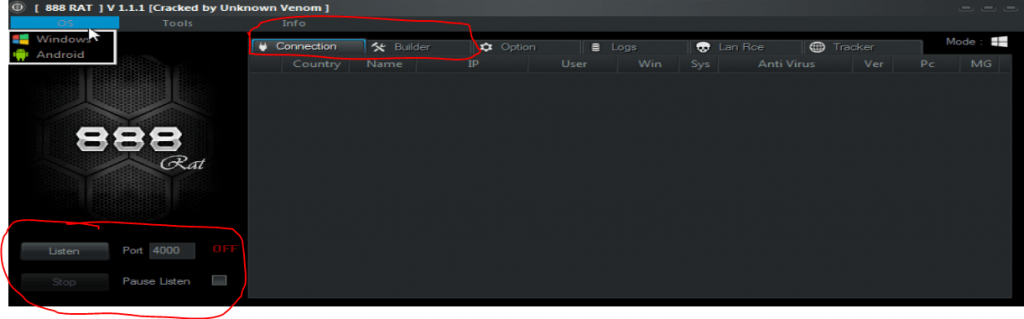
You have to click on listen before creating the payload. Connection and Builder options are very much useful in creating the payload as in the connection section you will get the information of the victim who has clicked your payload and in the builder section you will different options to create a payload and you will create the payload from this section only.
These many things are needed to create a simple payload as I am explaining to you about 888 rat I am not focusing on creating a perfect payload so this is a basic payload and can be detected at an advanced level you have to make an undetectable payload and bind it with some other option to gain victim trust and make him open the payload.
So In basic payload, this much of an overview is enough to create it.
Step-5 (Creating a Payload)
Select the platform for which you want to create a payload. I had chosen windows for it. Click on listen at the bottom. Then open the builder section under the info menu input the victim’s IP address then rest remains the same then check the install option below the info menu and click on create server.
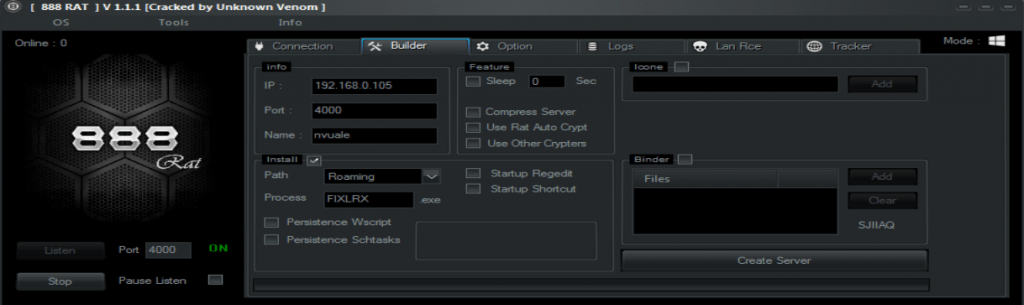
I have input my IP address as the victim IP address as here I want to run the payload in my same system.
A payload will be created after you clicked on create server option which will be available on the extracted folder. The payload is created when a message will pop up with the payload name stating that it has been successfully created.
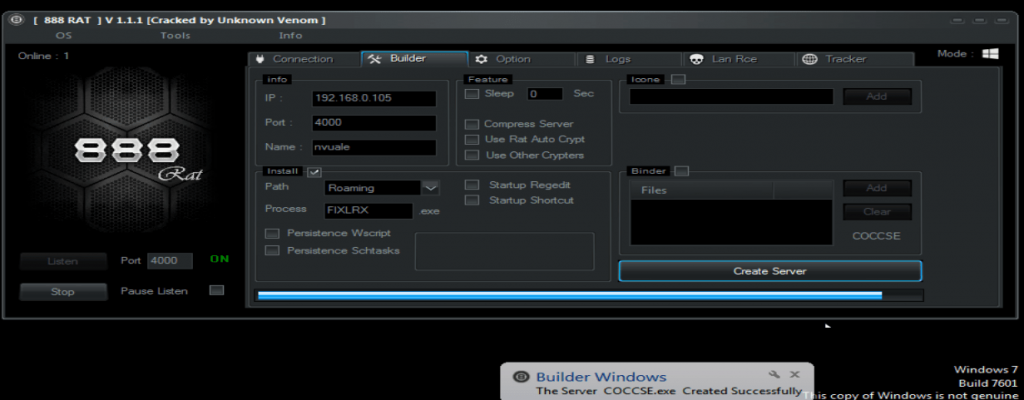
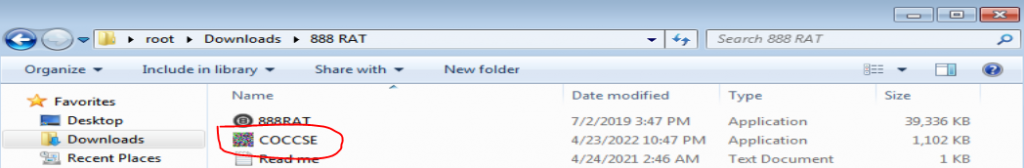
Now explore the folder location where you have extracted the folder. You will find the payload there with the name which has poped up in the message. In my case it is COCCSE.exe.
Open the file to get the connection. In the WAN case, you have to use social engineering and other attacks to send the payload to the victim and many other advanced techniques to get the victim to open the payload. Once the payload gets opened you will get the connection message popped up and in the connection option, you will be able to see the connection.
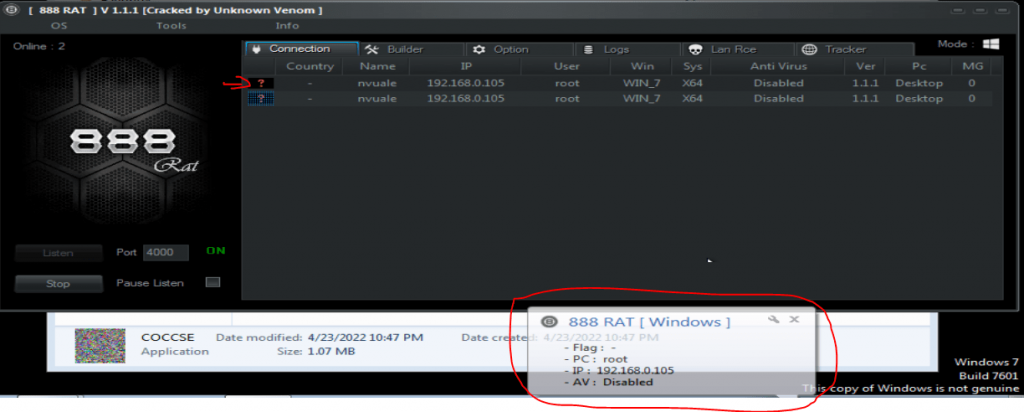
Once the connection is built then you have successfully hacked into the system using your payload so now you have many options to work with.
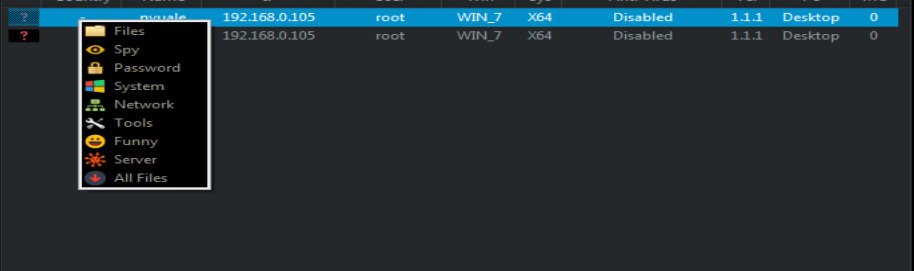
Right-click on the connection to see the option that can be performed. You can see here the number of options we get after a successful attack and you can use any of them.
In the password category, you will get an option to use a keylogger. If you don’t know what is a keylogger then you must read this – “Keylogger – The Surveillance Tool (2022)“.
Now for a demo purpose to make you see that it really works let us try to see the files present on the desktop of a victim in the 888 rat tool which we have already exploited.
Click the first option Files where we can get the details of the file then choose the desired location on which you want to see the existing file for me it’s desktop so I will go there.

Here you can see I got the details of my desktop files.
Step-6 (Closing)
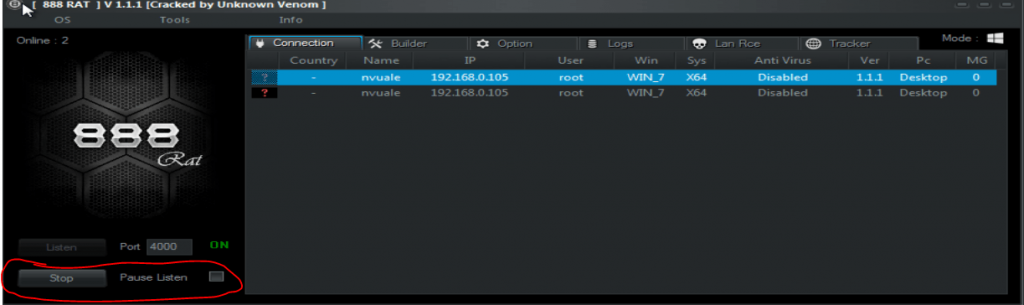
You can simply click on stop under listen or can use pause listen to stop the exploit and close 888 RAT.
I hope this example will help you to know what is 888 RAT and how it works. There are many tools that will help you to exploit this and create RAT such as Cypher RAT and many others.
NOTE- This article is only for educational purposes. Don’t misuse your knowledge and skills.
Download Cypher RAT, Other RATS
Visit our hacking category to learn more about hacking by clicking here.
If you want to know more about malware then click here.